Every layer of the stack we built over sixteen articles has a shadow. The electricity that powers data centers also powers the attacker’s servers. The software running your applications contains vulnerabilities. The networks routing your data route attack traffic just as efficiently.
In Processors and GPUs: How Chips Think, we covered the hardware layer. In How the Internet Actually Works, we traced packets from browser to server. In Software Fundamentals, we looked at how code runs. Each article described a layer of the stack.
This article is about how attackers move through those layers from the outside.
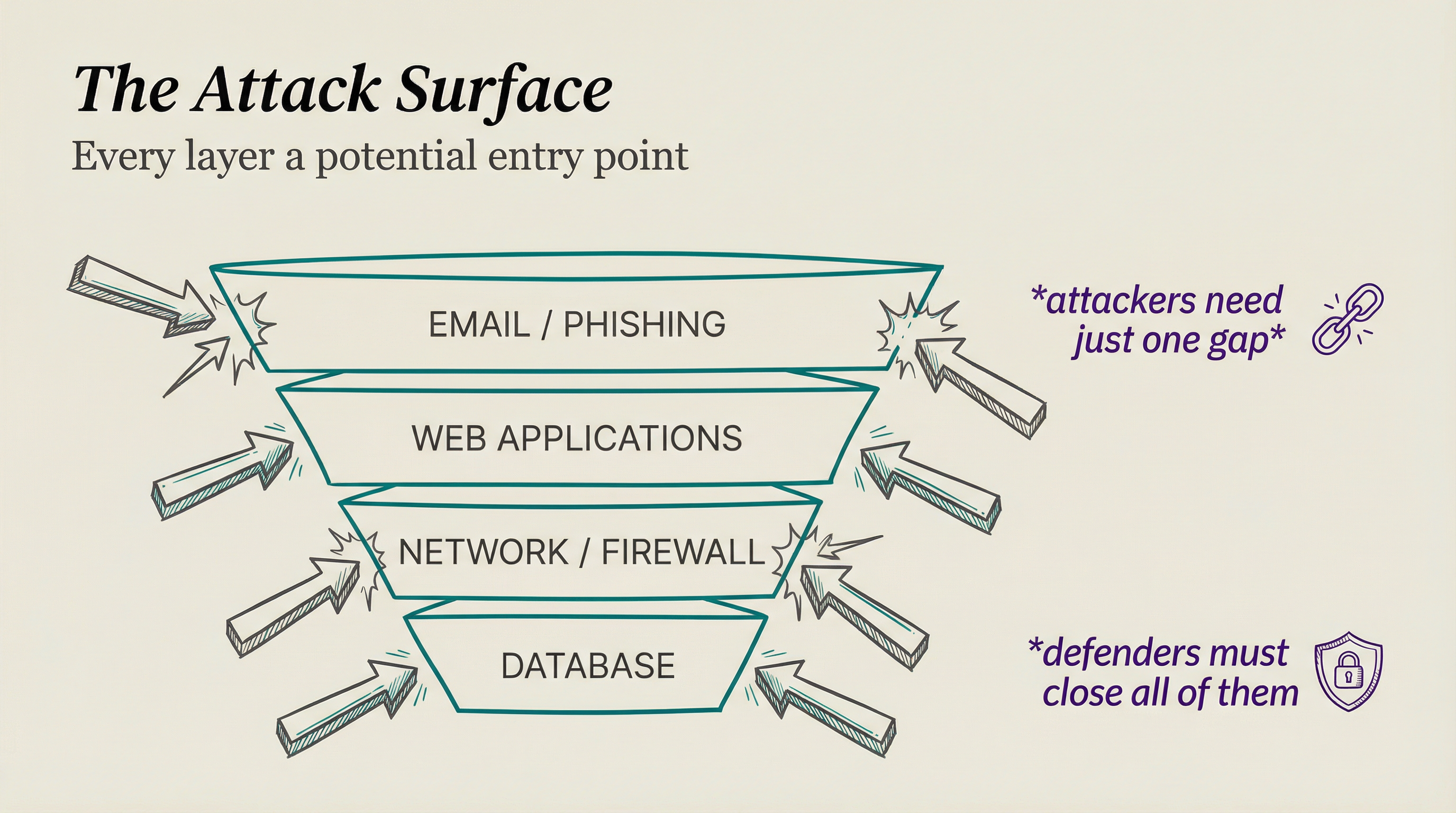
THE STACK AS AN ATTACK SURFACE
When security professionals talk about attack surface, they mean every point where an attacker could interact with your system. In a modern organization, that surface is enormous. A company running web applications has code vulnerabilities. That code talks to databases that can be manipulated.
Attackers do not need to discover a new layer. They need to find the weakest point in the layers you already have. A sophisticated attacker mapping an enterprise does not start by probing firewalls. They start by reading your job postings to learn what software stack you run.
They search LinkedIn for employee names. They check breach databases for credentials from previous incidents. They look up public DNS records and scan visible IP ranges for open ports.
Most of this is passive. The target has no idea it is happening.
HOW AN ATTACK UNFOLDS
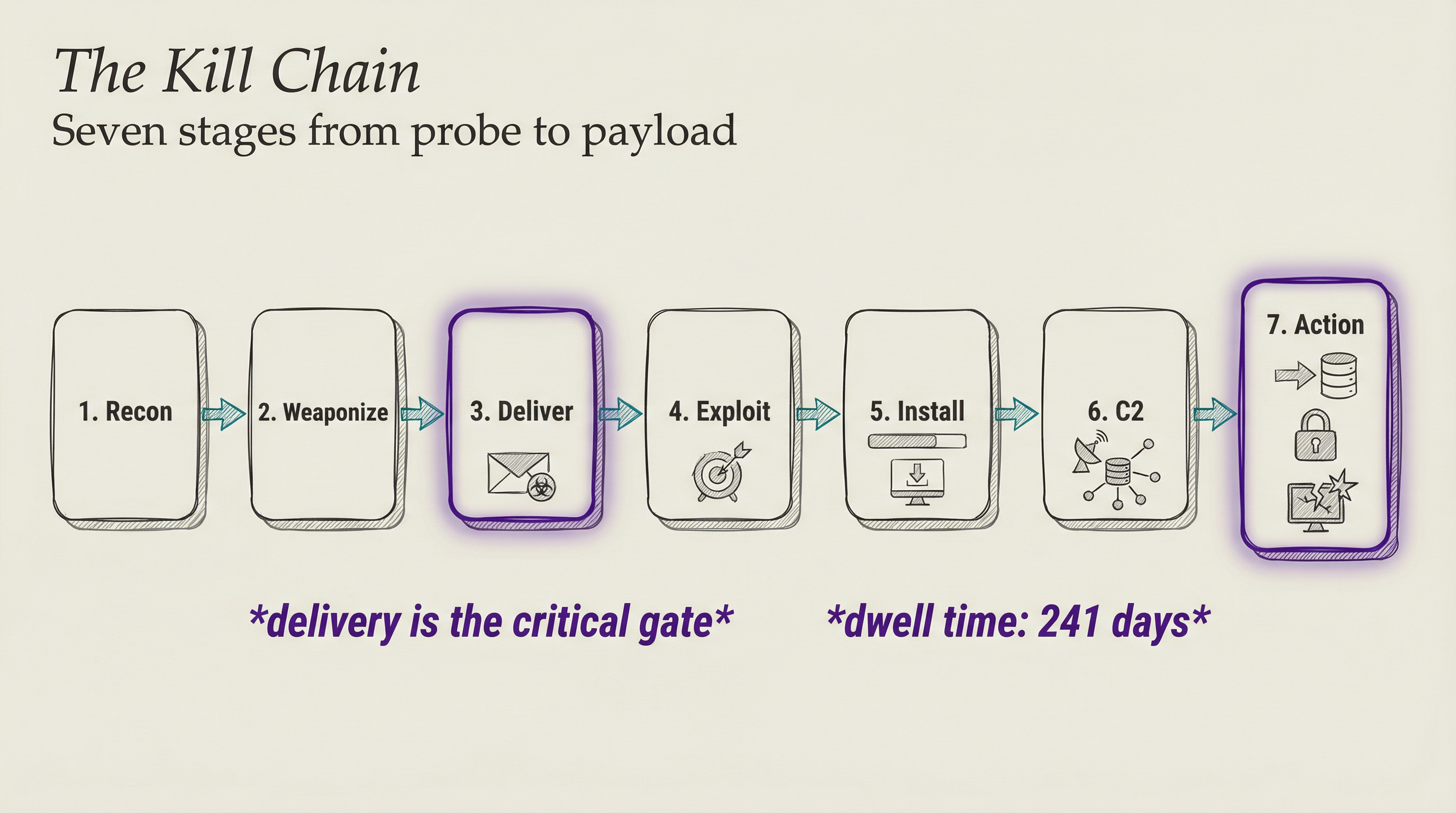
Most serious attacks follow a predictable sequence. Security researchers call it the kill chain, a term borrowed from military targeting doctrine. It has seven stages: reconnaissance, weaponization, delivery, exploitation, installation, command and control, and action on objectives.
Reconnaissance is the research phase. Weaponization is when the attacker builds or adapts a tool for the specific target. Delivery is the moment of contact, usually via email or a compromised website. Exploitation triggers the vulnerability.
Installation establishes persistence so the attacker survives a reboot. Command and control opens a channel back to the attacker’s infrastructure. Then the attacker does what they came to do.
Think of it like a locksmith’s workflow, reversed. A legitimate locksmith surveys the building, identifies the lock type, picks the right tools, gets through the door, and does the job. An attacker follows the same systematic process, just with different goals at the end.
THE DELIVERY PROBLEM
The hardest part of an attack is usually getting initial access. Once an attacker runs code inside your network, subsequent steps become easier because they operate from a trusted position inside the perimeter. Everything built to detect external threats now sits behind them.
This is why defenders focus so heavily on stopping delivery, and why attackers invest so much in making delivery look legitimate.
THE WEAPONS
PHISHING
Phishing targets the humans operating the systems rather than the systems themselves. The attacker does not need a flaw in your firewall if your CFO will wire $2 million to a fraudulent account after receiving a convincing email from what appeared to be the CEO.
Phishing was involved in roughly a third of data breaches in 2024. No vulnerability patch exists for human psychology.
Modern phishing targets specific people. A basic phishing message goes to millions with a generic lure. A spear phishing message targets a specific person, referencing real relationships, real projects, real context pulled from public sources. When a message references your actual manager’s name and a real client you work with, the signal that something is wrong becomes much weaker.
SQL INJECTION
SQL injection is purely technical. Web applications take input from users and build database queries from that input. If the application does not validate what the user types, an attacker injects SQL commands directly into the query.
The database runs those commands as if they were legitimate instructions.
The database trusts the application the same way a bank teller trusts a signed check. If someone forges the signature at the application layer, the database hands over the goods without questioning it.
Parameterized queries address this directly. They treat user input as data rather than executable code, so injected SQL commands never reach the query parser.
OWASP has listed SQL injection in its Top 10 most critical web vulnerabilities for over two decades. It keeps appearing because developers keep making the same mistake under deadline pressure.
SUPPLY CHAIN ATTACKS
Instead of attacking a target directly, the attacker compromises software the target already trusts. The SolarWinds incident in 2020 is the clearest example. Attackers inserted malicious code into an IT monitoring tool update, which reached 18,000 organizations including multiple US federal agencies.
The victims installed the backdoor themselves, as part of a routine update. The package carried a legitimate vendor signature. Nothing in the normal security workflow flagged it.
Supply chain attacks exploit trust that is usually warranted. You should update your software. You should trust signed updates from vendors. The attacker’s strategy is to make those correct behaviors work against you.
RANSOMWARE AS AN INDUSTRY
Ransomware encrypts your files and demands payment for the decryption key. The malware generates a symmetric encryption key, encrypts files across the system and network shares, and sends that key to the attacker encrypted with their public key. Then it deletes the local copy.
Without the attacker’s private key, the files stay locked. The cryptography is sound. The weakness is always in the delivery.
Ransomware has matured into a proper industry. Ransomware-as-a-Service platforms exist where criminal organizations build the malware, maintain payment infrastructure, and handle victim negotiations. Affiliates buy access and handle delivery. It operates like a franchise.
The economics are stark. The average ransom payment in 2024 reached $2 million.
The average total cost of a data breach in 2025 stands at $4.44 million globally, rising to $10.22 million in the United States.
Security researchers estimate the annual global cost of cybercrime at $10.5 trillion, exceeding the GDP of every country except two. These are not edge cases. This is a functioning economy built on top of the infrastructure we built.
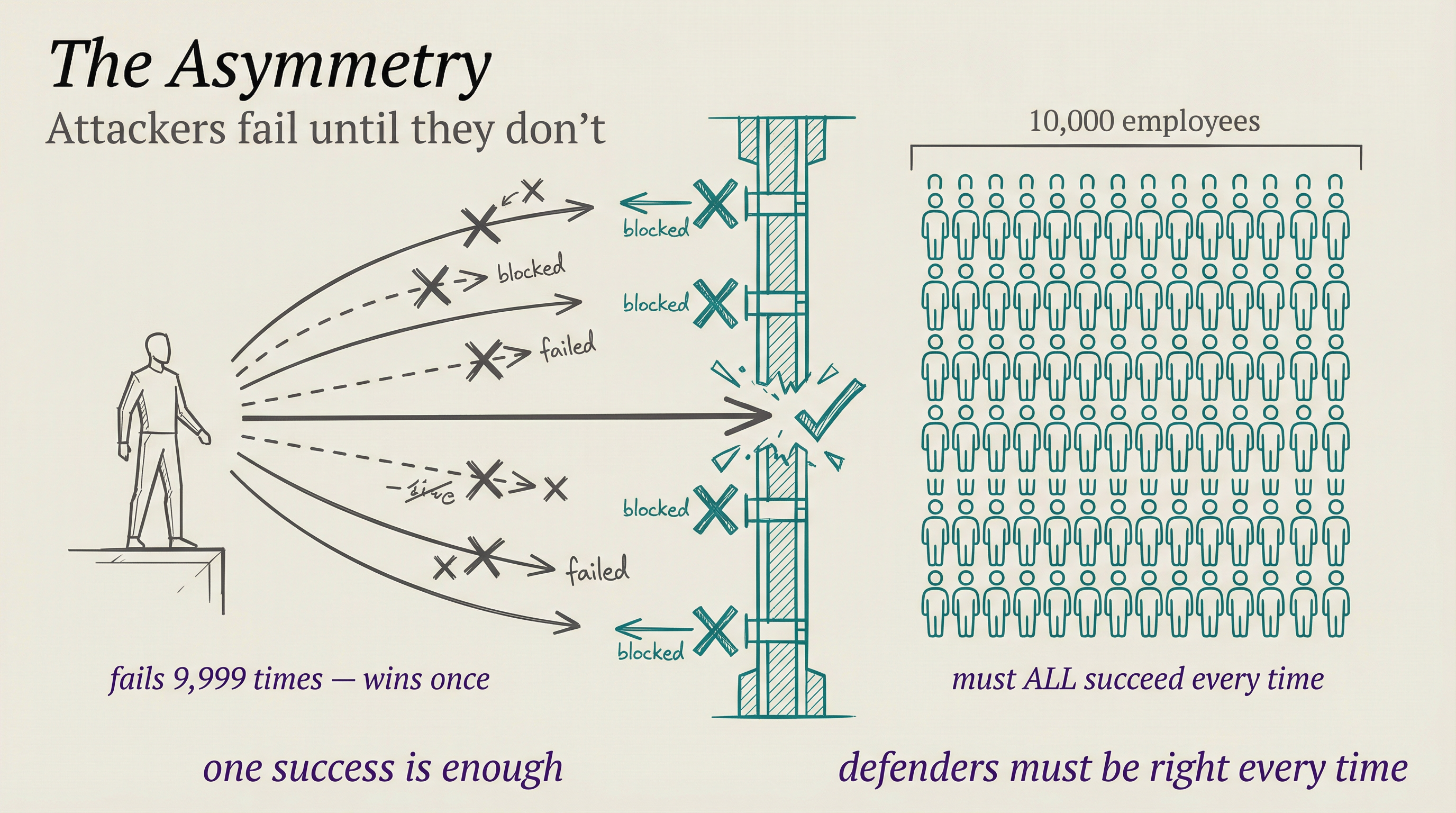
WHY DEFENSE IS HARDER THAN OFFENSE
Attackers need to find one way in. Defenders need to block all of them. This asymmetry is the defining challenge of the field and has no clean solution.
A company with 10,000 employees has 10,000 potential phishing targets. An attacker sending 10,000 emails needs exactly one person to click. The attacker can fail 9,999 times and still win.
The defender needs everyone to be right every time. That math never works in the defender’s favor.
The average time to identify and contain a breach was 241 days in 2025. Eight months during which an attacker may have been sitting inside a network, reading emails, mapping internal systems, and escalating privileges. Dwell time is how long an attacker has been inside before detection. Long dwell times give attackers time to understand your environment better than some of your own staff.
Defenders respond by layering controls. No single defense stops everything, but each layer raises the cost and complexity for the attacker. Network segmentation limits how far someone can move after gaining initial access. Multi-factor authentication means a stolen password is not enough.
Endpoint detection tools watch for behaviors that look like lateral movement or data staging. Logging everything means that when a breach happens, you can reconstruct what the attacker accessed.
I think the most underrated defense is patch management. Most successful attacks exploit known vulnerabilities with published patches. WannaCry ransomware in 2017 hit a Windows vulnerability for which Microsoft had released a patch two months earlier.
Organizations that had applied the patch were safe. The ones that had not lost billions.
Keeping software current is unglamorous work. It also stops a significant fraction of real attacks.
WHAT COMES NEXT
The series started with electricity. Then silicon, chips, data centers, networks, software, databases, machine learning, and the frontier labs racing toward AGI. Every one of those layers exists in the real world, operated by real humans, connected to external systems.
Attackers have been studying that stack as carefully as we have.
Cybersecurity is not a technical problem that gets solved. It is a continuous contest between the people who build systems and the people who look for gaps in them. Defenses improve. Attacks get more sophisticated.
The stakes keep rising as more critical infrastructure and financial systems move online.
Understanding how attacks work is the prerequisite for building harder targets and making better decisions about where to invest in defense.
Next up: Encryption and Trust: How Privacy Works Online, which covers the cryptographic machinery that makes secure communication possible at scale.
T.
References
- IBM Cost of a Data Breach Report 2025 - IBM’s annual analysis covering 604 organizations globally, with data on breach costs, detection timelines, and the financial impact of AI-driven security programs.
- Lockheed Martin Cyber Kill Chain - Original framework paper defining the seven stages of a cyberattack, developed by Lockheed Martin’s intelligence-driven defense team.
- OWASP SQL Injection - The Open Web Application Security Project’s reference on SQL injection mechanics, attack variants, and parameterized query defenses.
- Fortinet Cybersecurity Statistics 2025 - Aggregated statistics on attack volumes, breach costs, phishing prevalence, and attack trends across the global threat environment.
- CISA SolarWinds Advisory - Official US government advisory on the SolarWinds supply chain compromise, covering scope, indicators of compromise, and remediation guidance.