Posts
All the articles I've posted.
-
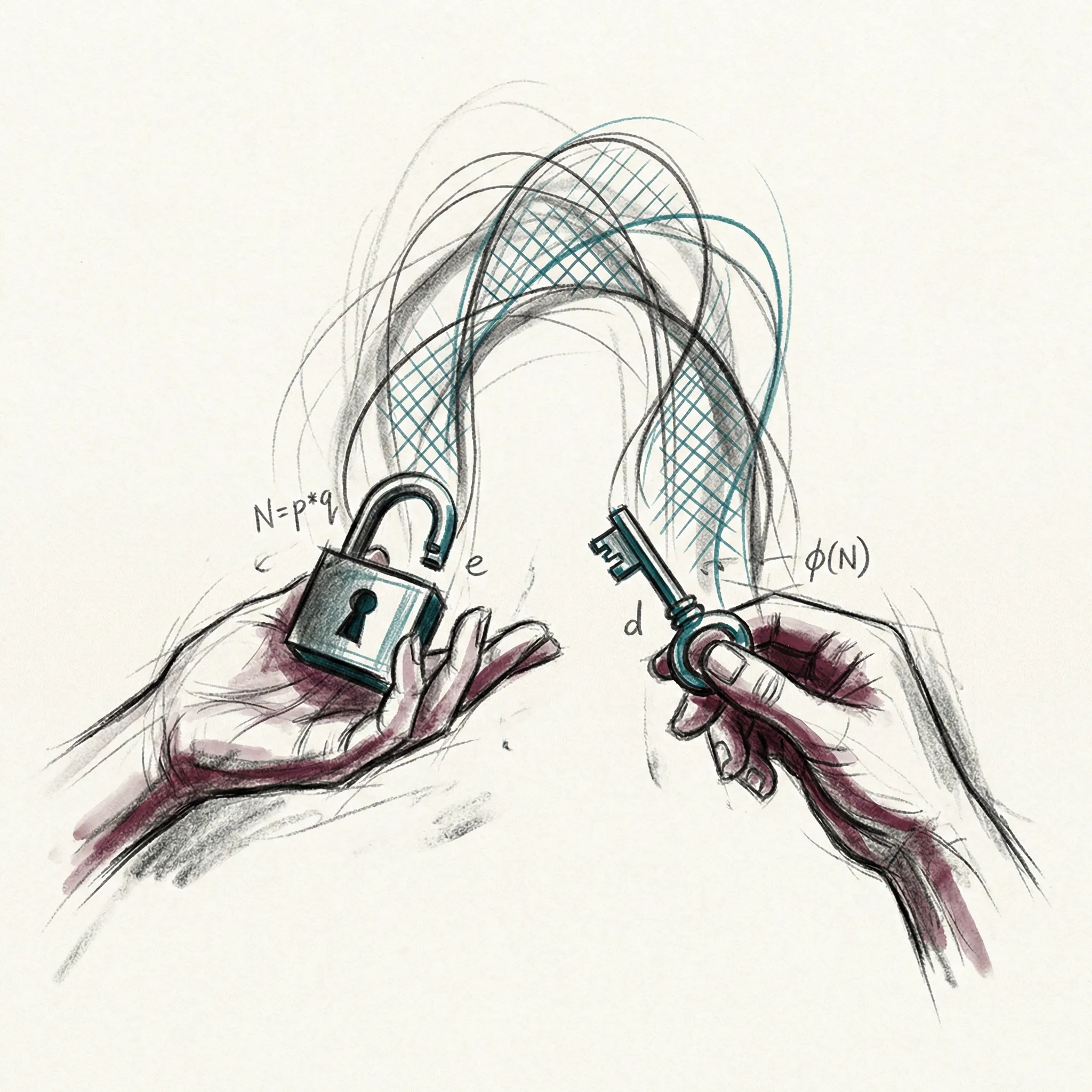 security8 min read
security8 min readEncryption and Trust: How Privacy Works Online
A clear walkthrough of TLS, public key cryptography, certificate authorities, and the chain of trust that keeps your browser sessions private.
-
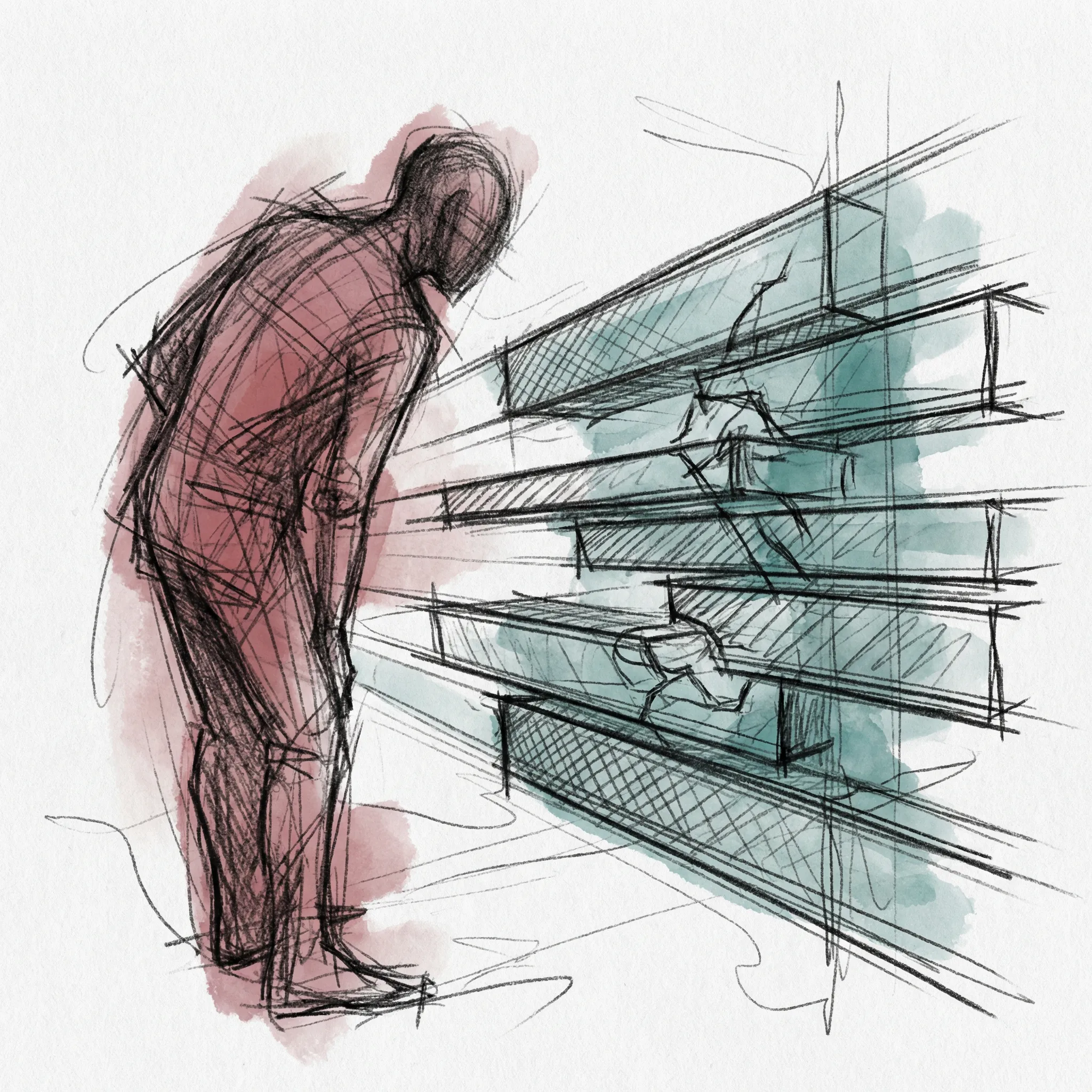 cybersecurity8 min read
cybersecurity8 min readHacking: How Cyberattacks Actually Work
The kill chain from first probe to final payload: how attackers move through a system, what tools they use, and why defenders are always fighting uphill.
-
 ai12 min read
ai12 min readThe Frontier Labs: Who Is Building AGI
The companies racing to build artificial general intelligence, their approaches, breakthroughs, and what sets each apart in 2025-2026.
-
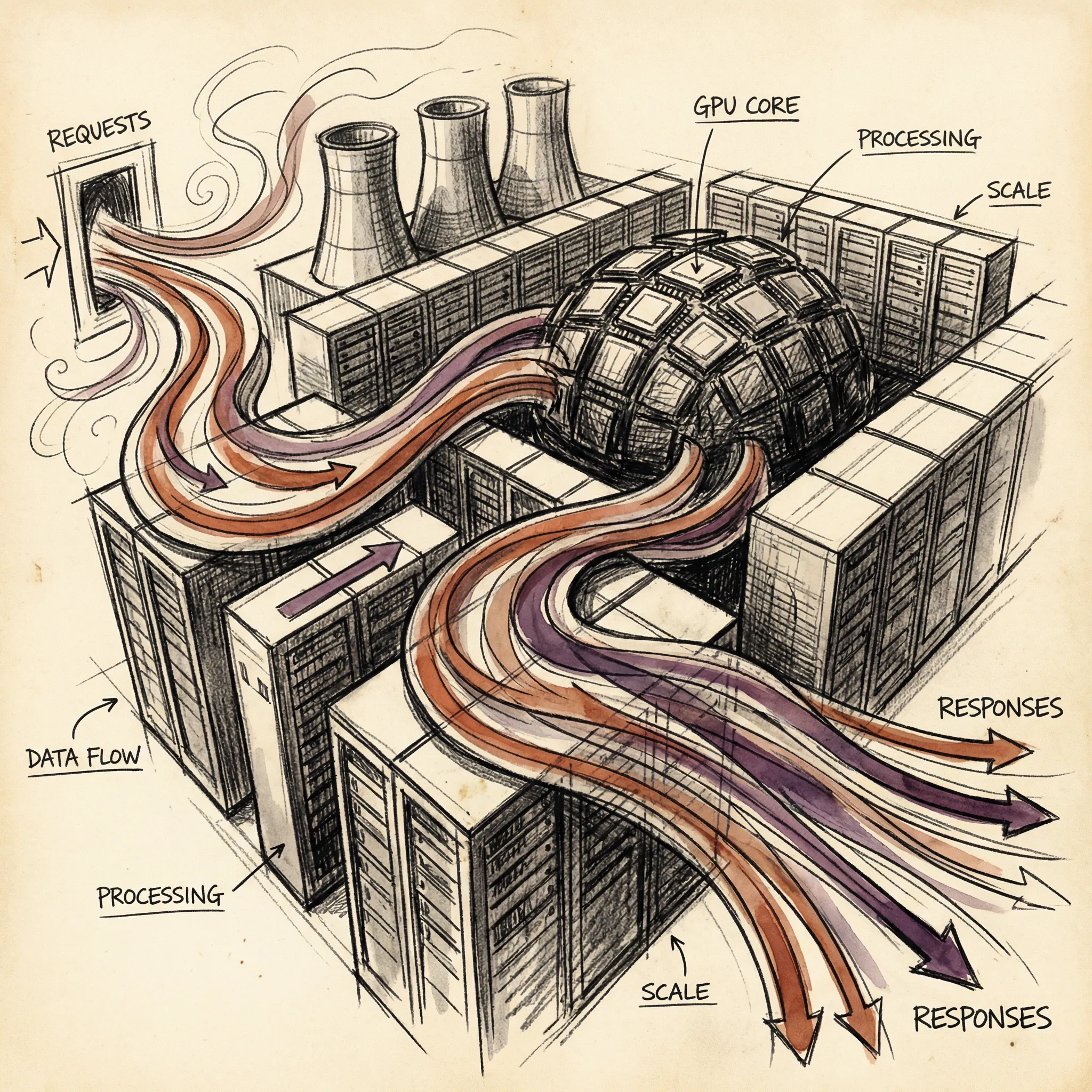 ai8 min read
ai8 min readAI Inference and Scaling: From Training to Serving Billions
How trained AI models serve billions of requests through inference optimization, scaling infrastructure, and cost engineering.
-
 ai9 min read
ai9 min readAI Training: How Models Get Smart
How AI training works, from gradient descent and backpropagation to RLHF, synthetic data, and the emerging possibility of recursive self-improvement.
-
 ai10 min read
ai10 min readLLMs - How ChatGPT Actually Works
How large language models actually work, from tokenization and embeddings to attention mechanisms and next-token prediction.
-
 neural-networksUpdated: 11 min read
neural-networksUpdated: 11 min readNeural Networks: How AI Mimics the Brain
How artificial neurons combine into networks that recognize images, understand language, and generate text. From perceptrons to transformers.
-
 machine-learning12 min read
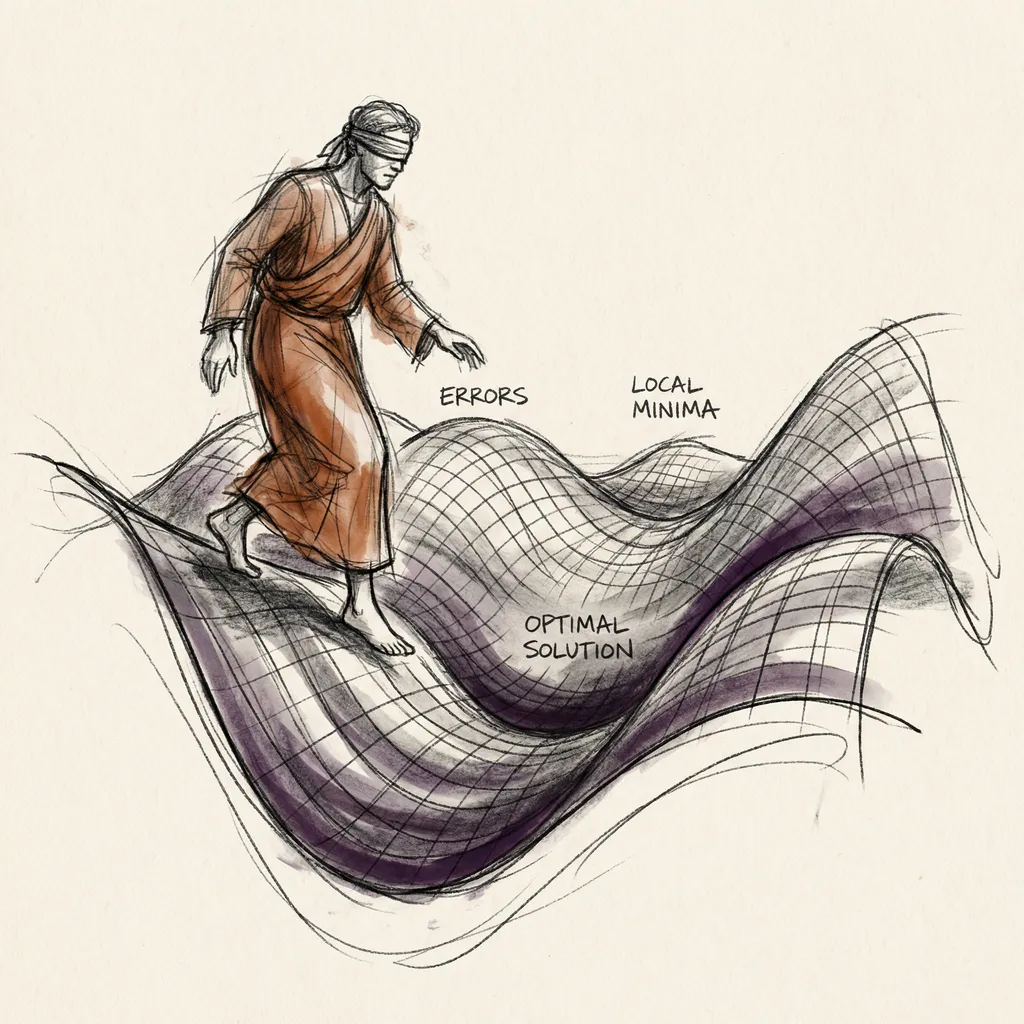
machine-learning12 min readMachine Learning: How Computers Learn from Data
How computers find patterns without being told the rules. Supervised learning, gradient descent, and why data quality matters more than algorithms.
-
 databases5 min read
databases5 min readDatabases and Data: How Information Is Stored
How databases store, organize, and retrieve data at scale, from SQL tables and B-tree indexes to vector search powering AI.